Unlocking Dunzo's Internal Dashboard

Hello Everyone!
This write-up is about Dunzo's Sensitive Information Disclosure Vulnerability.
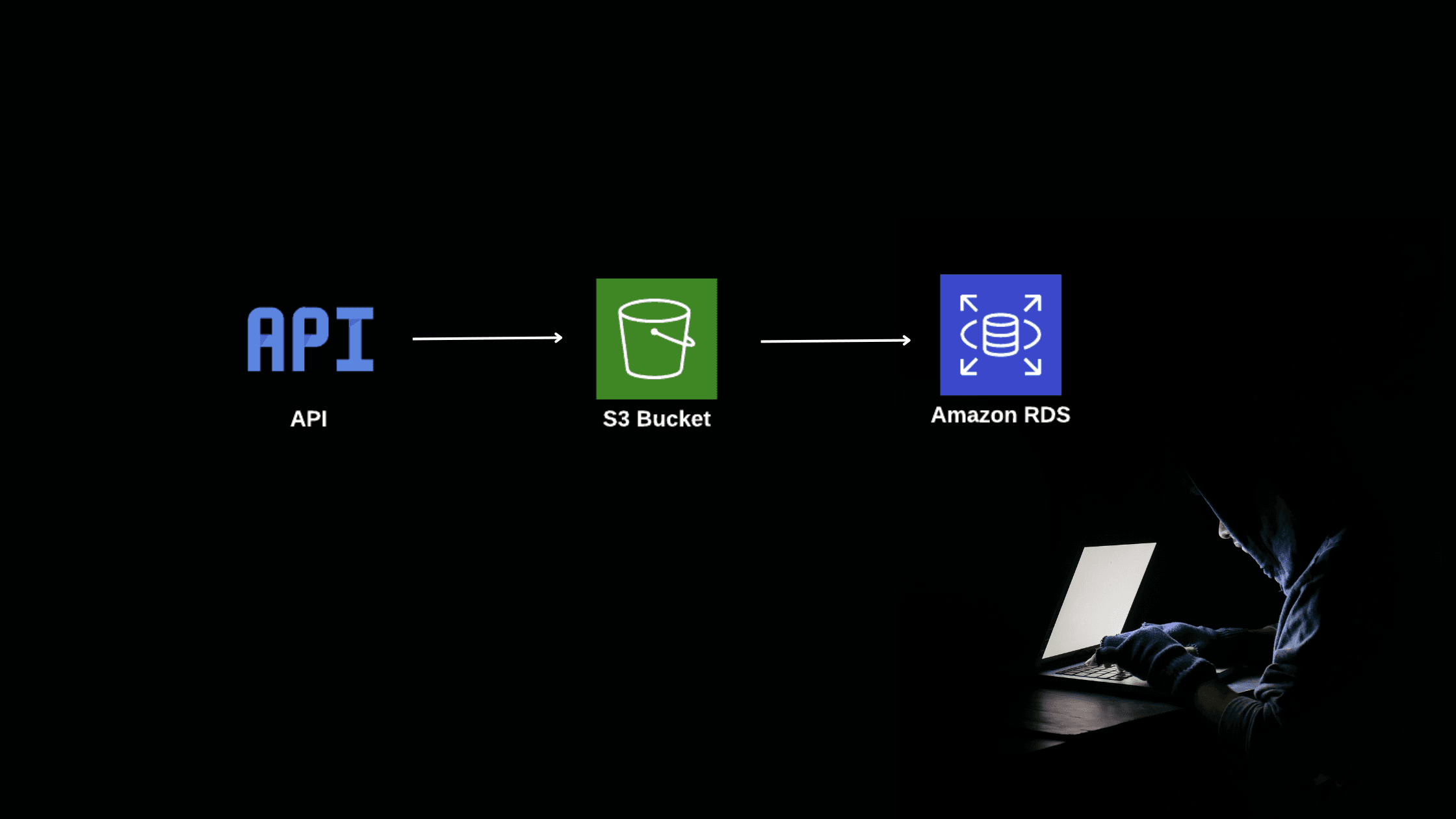
The vulnerability could have allowed an attacker to access the internal monitoring dashboard of Dunzo.
Subdomain Enumeration:
I started with subdomain enumeration. For subdomain enumeration, I used crt.sh.
What is crt.sh:
It’s a web interface. that lets you search for certs that have been logged by CT.
In this case, I got only a few subdomains. So I manually checked each subdomain. If you found a large number of subdomains you can use the Httpx tool from project discovery.
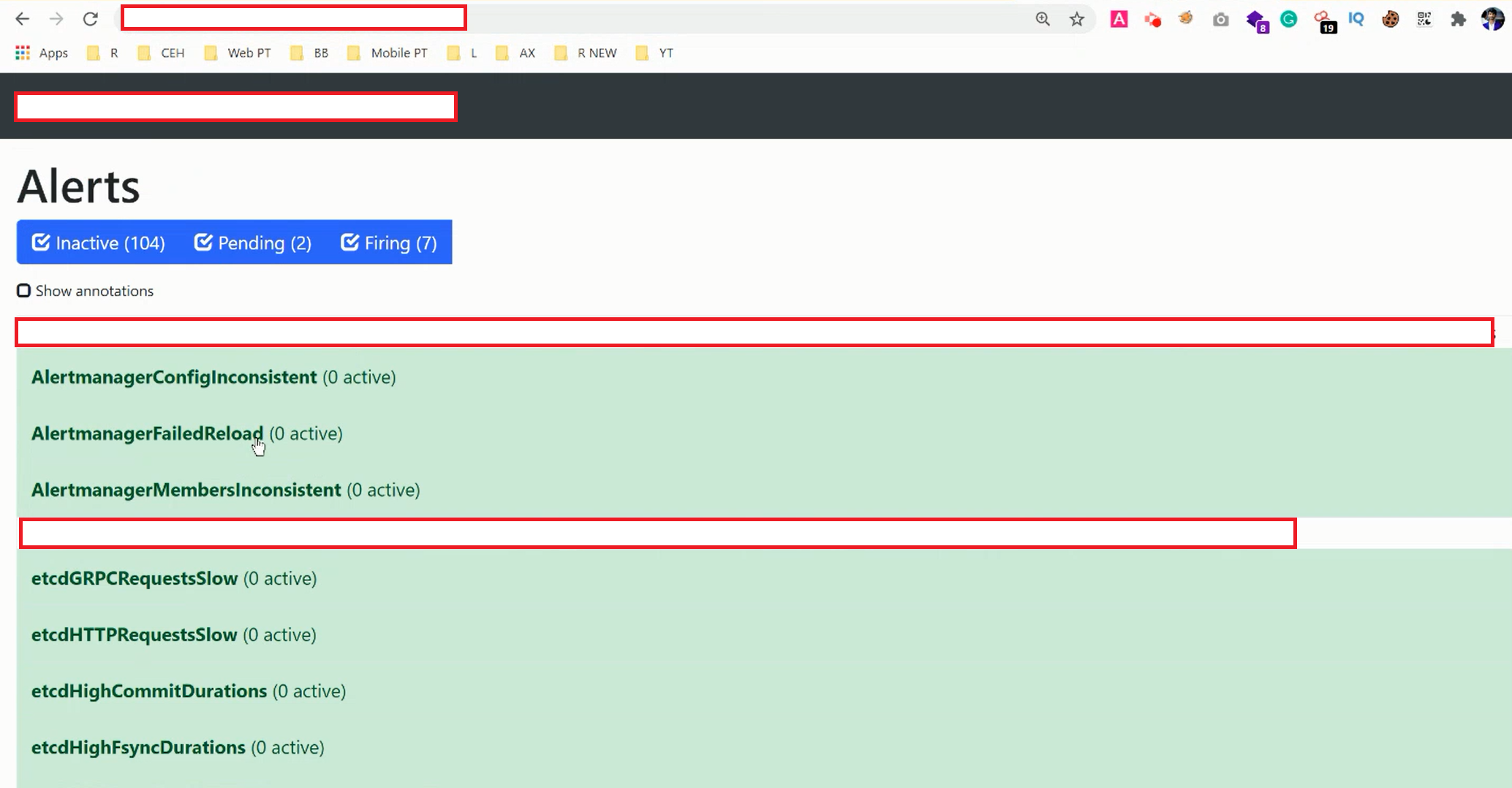
One of those domains I can access the internal dashboard without authentication. Here I got the internal IP and production server logs .
POC of my findings

Report Timeline:
Mon, 11 Jan 2021 - Reported to Dunzo Security Team.
Mon, 11 Jan 2021 - Immediately got a response from the team
Tue, 12 Jan 2021 - Issue Fixed
Tue, 12 Jan 2021 - Re-tested and confirmed the fix
Tue, 12 Jan 2021 - Got an Appreciation from the Dunzo Team